Just thinking that someone may have violated your privacy by accessing your computer makes you feel chills. But how do I know if someone has entered my PC? Fortunately, there are some obvious signs that someone has been snooping on our computer. In addition, we can have some tricks to get more information about it. Do not miss all the ways you have to know if this has happened or not below, we will answer your question about how do I check recent activity on my computer so that you can take the necessary measures.
How do I check recent activity on my computer?
You will need a computer, an internet connection.
Step 1:
First of all, it is important that you know what items the intruder has been able to access. Most commonly, an intruder wants to do one of the following:
- Change or delete data found on the computer.
- Copy data also hosted on the computer.
Fortunately, intrusions leave their mark through certain logs (network, event, application), running processes, file systems, and local configuration files.
You may also like to read, chromecast without wifi. To know more visit our blog http://techconnectmagazine.com/.
Step 2:
One of the steps we will take is to check the logs. In Windows, this is found in the event viewer, in Control Panel – Administrative Tools. Each event has an associated date and time, so although it may be tedious or complex to understand, the times can be key for you.
In Linux, you can also consult them. For this, you can access the / var/log/directory as a superuser and view the logs.
On Mac, the procedure is very similar to the previous operating systems: we must open the console to see the contents of the files in the /private/ var/log folder.
Keep in mind that, by reviewing the records, you may come across actions that, even if you do not know what they are at first, will give you the clue if, for example, you were not using the computer at those recorded moments. So, if you were wondering how to know if someone has copied files from your computer, you already know that this is a good method.
Step 3:
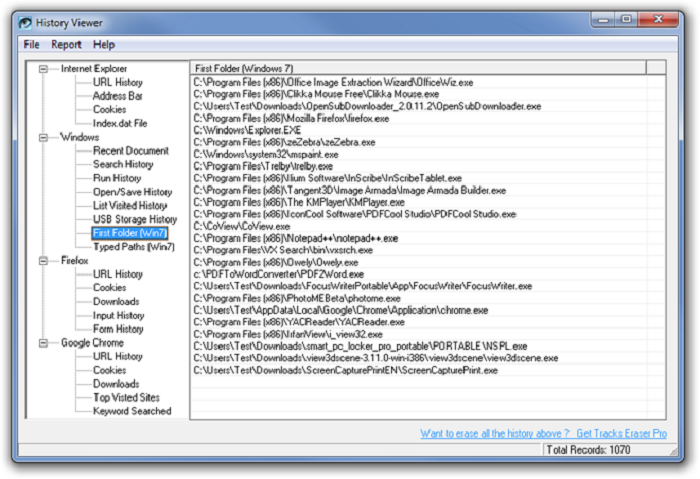
Another step to take is to review the records of certain programs. For example, in browsers, we can check to browse history, search, cache …
We can also control the logs of the router by accessing its settings. Remember that access to this is different in each router model and is protected by a password.
Another interesting action is to use some tool to see the DNS records. These are the browsing requests made by our computer. If we have not done it, we already know that someone has accessed it.
Step 4:
Another way to see what has happened on our computer recently is by using the Recent Items option. To access it, we have to type in the search box “Run”, and press the Enter or Enter key. After this, a small window will open where we can write the command we want to execute. In this case, it will be ” Shell: Recent ” (we must write it as it is written but without the quotes). In this way, we obtain the information about the elements that have been modified and, everything that we have not modified, the intruder has had to do and, in this way, you will know if someone has entered your PC.
We can also check if USB devices have been plugged in using different free tools. So this is another reliable way to tell if someone has possibly downloaded files from your PC.
Step 5:
On some occasions, an intruder has been able to leave keyloggers or remote access applications to collect data. Usually, this type of malware can be detected with a scan made by an antivirus program.
If you suspect that there is some malware running (it is usually noticed because the computer is more unstable than usual) you can ensure by checking what is currently working on the computer using Task Manager. This is not so easy, so it is recommended that you regularly check the processes that are usually active on your computer while you have no problems or suspicions of any kind. In this way, when there is a strange process, you will know how to recognize it.
You may like also to read https://whizowl.co.uk/